Thursday, March 28, 2013
Tuesday, March 26, 2013
C# 4.5 and CLR Revolution
C# Generation Next
CLR Inside
Courtsey Maoni Stephen's White paperhttp://blogs.msdn.com/b/dotnet/archive/2012/07/20/the-net-framework-4-5-includes-new-garbage-collector-enhancements-for-client-and-server-apps.aspx
1. Background Server Garbage Collection
Before version 4, the .NET Framework provided a concurrent GC mode that performed full GCs concurrently with user code (vs. blocking, which pauses all user threads), thus reducing pause time for full GCs. This mode was available only for workstation GC.
In the .NET Framework 4, we delivered an improved version called the background workstation garbage collection, which reduced latency but only benefited client apps.
In the .NET Framework 4.5, we have delivered background server garbage collection, which is typically used for server apps. As a result, all apps now have background GC available to them, regardless of which GC they use.
Backgorund GC Operation
2. GC Collect Inversely Proportional to Throughoutput Balanced LOH
More GC collect less throughoutput.Vice versa
Common Root Cause for above IMBALANCE GC HEAP
For server GC, GC trigger when heap runs out of allocation.
1 Logical processors have 1 heap.
In one application server there are many worker processors which spuns many threads and these threads in turns consume memory.
In the .net framework 4, small object heap memory allocation is balanced where as LOH is not balanced due to which the GC triggers lot.
In the .net framework 4.5,SOH and LOH are balanced hence it triggers less GC.
3.Support Large Dataset >2GB
We can now able to process array with large dataset. It is configured using
4. Reuse free available memory after GC collect.
In earlier releases of the .NET Framework, once a memory block was rejected as a candidate for an allocation, it was removed as a candidate for subsequent allocations.
In the .NET Framework 4.5, we now retain free memory blocks as candidates for allocation requests until they are used. The new algorithm uses LOH space much more efficiently, leading to decreased fragmentation and memory use.
5. SustainLowLatency- Avoid Full blocking of GC
While the SustainedLowLatency setting is in effect, generation 0, generation 1, and background generation 2 collections still occur and do not typically cause noticeable pause times. A blocking generation 2 collection happens only if the machine is low in memory or if the app induces a GC by calling GC.Collect().
6. NUMA-Non uniform Memory Access, Black box for me.
Unable to understand the basic fundamentals of it. If someone can flash few reference to help me understand this. Regret for Ignorance on this subject.
Monday, March 25, 2013
Sunday, March 24, 2013
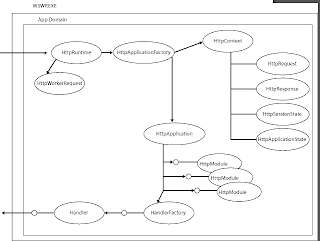
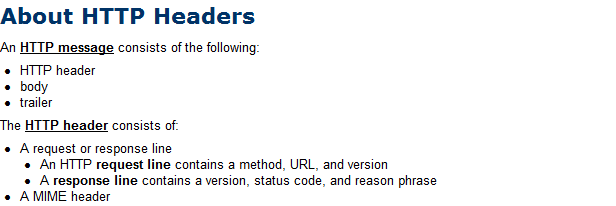
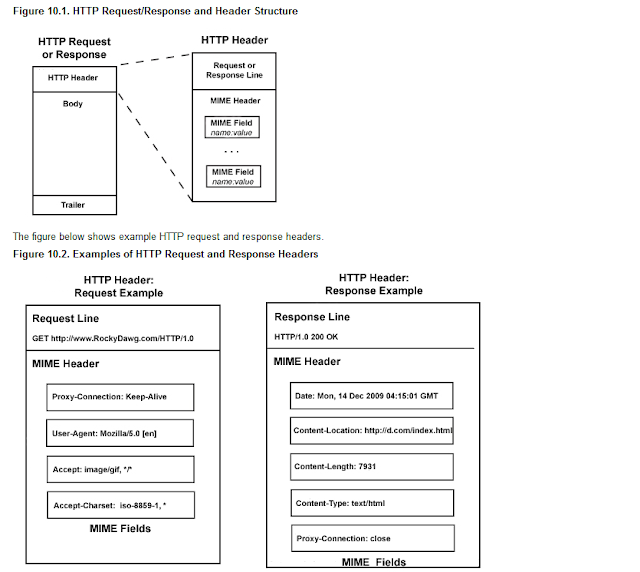
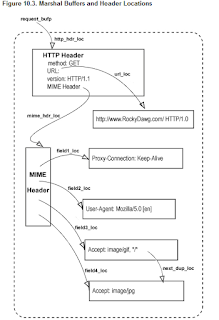
Asp.net Pipeline , httpcontext And IIS 7.5 integrated Mode
Asp.net request pipeline mode is something that each asp.net developer must know. Its difficult to memories or understand the concepts because IIS and .net framework is going through radical changes very often. Still we must touch base few basics. All I want one to go through HttpRuntime, Httpcontext, Httpapplication , Httpmodule and HttpHandler. If we clearly understands its flow with respect to IIS handling we will be able to troubleshoot any issues or create any custom pipeline based on this.
For e.g IIS integrated mode support httpcontext.current.request.header.add()...
HttpContext deals with response, server, requests, error, session , application
HttpModule deals with application startup authorization, authentications etc.
HttpHandler based on file extension we can set events to perform.
HttpRuntime decides configuration such as request length, queue length, Querystring and so on.
For e.g IIS integrated mode support httpcontext.current.request.header.add()...
HttpContext deals with response, server, requests, error, session , application
HttpModule deals with application startup authorization, authentications etc.
HttpHandler based on file extension we can set events to perform.
HttpRuntime decides configuration such as request length, queue length, Querystring and so on.
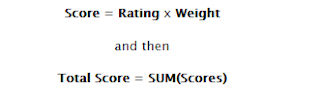
Decision Analysis and Resolution Matrix Called as DAR
For e.g we want to setup Virtualization so we have many options for us to evaluate before we decide on technology. Say for example..In case of VDI...virtual desktop environment, we have various options available such as Virtual machine based on Virtual pool, Remote desktop session based or virtual machine session based. Now if want to choose the best possible solution then we need to have a all relevant factors or parameter to evaluate against. Here in this case we can evaluate the options against scalability, availability, performance, maintenance, consistency, cost etc...
For any architect , it is very essential that one knows about such tools or methods to evaluate it. At the end steering or management committee needs statistics and full proof solution to support their decision even. What If I say something right? will that make sense to world ? The answer is Big 'NO'. The business is driven based on facts and figure.
 |
| Fig 1 |
DAR Matrix
Friday, March 22, 2013
Thursday, March 21, 2013
IIS 7.5 Load User Profile = true for Registry issue due Windows User Profile service
Today was strange day for me. It all started with trouble in the paradise. We recently did deployment of small changes in MS commerce server 2007 and EPI server. Now wcf service and website hosted in IIS 7.5. With main website having virtual directory pointing EPI server content management system.
Cut Long story short-
We checked the event log viewer for the root cause..And below was the whole script...
This event is letting us know that when the profile was being unloaded w3wp.exe with process id (PID) 1956 had a registry key handle to the profile hive for the user with SID S-1-5-21-2641105361-2081720548-7543625-1000.
Cut Long story short-
We checked the event log viewer for the root cause..And below was the whole script...
In the Application Event log, the following event was logged:
Log Name: Application
Source: Microsoft-Windows-User Profiles Service
Date: 2010/5/31 13:10:01
Event ID: 1530
Task Category: None
Level: Warning
Keywords:
User: SYSTEM
Computer: ComputerName
Description:
Windows detected your registry file is still in use by other applications or services. The file will be unloaded now. The applications or services that hold your registry file may not function properly afterwards.
The following information was included with the event:
2 user registry handles leaked from \Registry\User\S-1-5-21-3837118448-4114559512-2412068830-1006_Classes:
Process 1956 (\Device\HarddiskVolume2\Windows\SysWOW64\inetsrv\w3wp.exe) has opened key \REGISTRY\USER\S-1-5-21-3837118448-4114559512-2412068830-1006_CLASSES
Process 1956 (\Device\HarddiskVolume2\Windows\SysWOW64\inetsrv\w3wp.exe) has opened key
The problem was due...
If you have other application pools even they will use the same c:\windows\temp folder. If you set the option to load the user profile the temporary directory will be now change to use the profile’s temporary folder C:\Users\apppooluserid\AppData\Local\Temp.
If the profile is loaded you also have access to all the custom environment variables for that user.
Here’s a question what do you think will the temporary folder be when the Application Pool identity is set to Network Service and Load User Profile is set to True ?
It is not C:\Users\NetworkService\AppData\Local\Temp. but C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp
Here’s a question what do you think will the temporary folder be when the Application Pool identity is set to Network Service and Load User Profile is set to True ?
It is not C:\Users\NetworkService\AppData\Local\Temp. but C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp
According to kb947239, event 1530 occurs because Windows automatically closes any registry handle to a user profile that is left open by an application.
In previous versions of Windows, we need to download and install the User Profile Hive Cleanup Services (UPHClean) to ensure user sessions are completed terminated when a user logs off. So in Windows 2003 IIS6, UPHClean isn’t downloaded by default.
After Windows Vista, UPHClean utility is built into User Profile service which always runs. On Windows 2008, UPHClean removes access to files or directories data that was cached by the application for the file is lost. This could cause the process to fail because it cannot read from the file. This issue seems to be improved in UPHClean v2.0.
The solution to preventing this problem turns out to be a very simple configuration setting in IIS7's Application Pool Advanced Settings.
Lucky for us, the issue was resolved after enabling Load User Profile in Application Pool setting.
IIS doesn't load the Windows user profile, but certain applications might take advantage of it anyway to store temporary data. What this does is tell IIS to completely load the user profile for the entirety of the execution of the application.
Thank God...It just saved my day....
Wednesday, March 20, 2013
Its all about IIS 7.5 .You must know
We got two important parts in IIS 7.5
Integrated Mode : I called it as Http Module Pipeline
Classic Mode : More of ISAPI
Further isolation:
User Mode: IIS Log
Kernel Mode : Refer HTTErr log..in windows/system32/LogFiles/..
One can use log parser to analyse the logs and find the root cause of the problem.
Important App Pool Settings:
applicationHost.config file ( Found in location: C:\Windows\System32\inetsrv\config)
ApplicationHost.config is the root file of the configuration system when you are using IIS 7 and above. It includes definitions of all sites, applications, virtual directories and application pools, as well as global defaults for the web server settings (similar to machine.config and the root web.config for .NET Framework settings).
IIS Windows Process Activation Service (WAS)
Windows Process Activation Service (WAS) manages application pool configuration and the creation and lifetime of worker processes for HTTP and other protocols. The World Wide Web Publishing Service (W3SVC) and other services depend on WAS.
Integrated Mode : I called it as Http Module Pipeline
Classic Mode : More of ISAPI
Further isolation:
User Mode: IIS Log
Kernel Mode : Refer HTTErr log..in windows/system32/LogFiles/..
One can use log parser to analyse the logs and find the root cause of the problem.
Important App Pool Settings:
- Request Queue length Limit : Default 1000..
- Overlap App pool recycle.
- No of Worker processor.
- Switch off Asp.net debug mode off..
- Regular Interval of App Pool Recycle.
applicationHost.config file ( Found in location: C:\Windows\System32\inetsrv\config)
ApplicationHost.config is the root file of the configuration system when you are using IIS 7 and above. It includes definitions of all sites, applications, virtual directories and application pools, as well as global defaults for the web server settings (similar to machine.config and the root web.config for .NET Framework settings).
IIS Windows Process Activation Service (WAS)
Windows Process Activation Service (WAS) manages application pool configuration and the creation and lifetime of worker processes for HTTP and other protocols. The World Wide Web Publishing Service (W3SVC) and other services depend on WAS.
| Name | Description |
|---|---|
| IIS Application Pool | An Internet Information Services (IIS) application pool is a grouping of URLs that is routed to one or more worker processes. Because application pools define a set of Web applications that share one or more worker processes, they provide a convenient way to administer a set of Web sites and applications and their corresponding worker processes. Process boundaries separate each worker process; therefore, a Web site or application in one application pool will not be affected by application problems in other application pools. Application pools significantly increase both the reliability and manageability of a Web infrastructure. |
| IIS Protocol Adapter | An Internet Information Services (IIS) protocol adapter is a Windows service that receives messages on a specific network protocol and communicates with The Windows Process Activation Service (WAS) to route incoming messages to the correct worker process. http://msdn.microsoft.com/en-us/library/ee377050.aspx |
Tuesday, March 19, 2013
Monday, March 18, 2013
Tuesday, March 12, 2013
Virtual Desktop Infrastructure Windows 2012 Server Hyper-V Virtual Machine Installation and Setup
What we get?
- Using virtual machine we can have independent isolated dev environment for each developer. Virtualize in terms of RAM and processor.
- Easy to enable new Virtual machine through template or image file i.e VHD.
- Easy to manage through system center 2012 i.e remote desktop services web enabled.
- Factors to be considered.
- Windows update.
- Anitvirus installation
- Software Licencing
- Security patches
- Backup strategy
- External data storage for developer. External drive to save file
Primary Server
OS : Windows Server Core 2008 R2
16 GB Ram Processor 4 GHz speed
VM1: 4 GB /1 Processor
VM2: 4 GB/1 Processor
VM3/VM4
Alternative to VDI: Remote Development server Session based RDP.
Is to enable Remote Destop Session based user option. This comes handly and just require to add limit to session users. No installation at all. All users will be having same set of underlying software and feature. Any changes to environment will affect all users and environment. Good in response widely used and opted.
Monday, March 11, 2013
Coding Tips and Tricks
Cyclic Constructor in C#
public class Car
{
//Private Member
private int m_CarID=int.MinValue;
private string m_CarType=string.Empty;
private string m_CarName=string.Empty;
private string m_Color=string.Empty;
private string m_Model=string.Empty;
//Constructor
public Car()
{
//default Constructor
}
//Parameterized Constructor
public Car(int carID, string carName)
{
m_CarID = carID;
m_CarName = carName;
}
//Cyclic Constructor
public Car(int carID, string carName, string carType,string carModel):this(carID,carName)
{
m_CarType = carType;
m_Model = carModel;
}
//Cyclic Constructor
public Car(int carID, string carName, string carType, string carModel,string color)
: this(carID, carName,carType,carModel)
{
m_Color = color;
}
}
static void main()
{
Car objCarA=new Car();
Car objCarB=new Car(1,"matiz");
Car objCarC=new Car(1,"matiz","SmallCar","2000");
Car objCarD=new Car(1,"matiz","SmallCar","2000","Dark Green");
}
Validation to Check for Comma separated EmailIDs
List of Email ids separated with [,] Email ID may contain character set as [._-']
^((\w+([-_.']\w+)*@\w+([-_.']\w+)*\.\w+([-_.']\w+)*)*([,])*)*$
Finite automata rule Values should proceed with email Ids with Comma Separated. No comma will precede the email IDs.
abc.xyz@anonymous.com
abc.xyz@anonymous.com,abc-xyz@anonymous.com,abc_xyz@anonymous.com
abc.xyz@anonymous.com,com,D'Souza@anonymous.com
abc.xyz
,abc.xyz@anonymous.com
abc.xyz@anonymous.com,
abc
Javascript
function CheckForCommaSeperatedEmailIDs( fieldValue )
{
var regex = /^((\w+([-_.']\w+)*@\w+([-_.]\w+)*\.\w+([-_.]\w+)*)*([,])*)*$/;
if( !fieldValue.match( regex ) )
{
alert('The Email IDs Invalid');
return false;
}
return true;
}
Validation to check UserID with Period/Dot seperated
1) Ratan.Tata
2) Anil.Dhiru.Ambhani
Ratan.
1) .Mukesh.
2) Amir.khan.
public class Car
{
//Private Member
private int m_CarID=int.MinValue;
private string m_CarType=string.Empty;
private string m_CarName=string.Empty;
private string m_Color=string.Empty;
private string m_Model=string.Empty;
//Constructor
public Car()
{
//default Constructor
}
//Parameterized Constructor
public Car(int carID, string carName)
{
m_CarID = carID;
m_CarName = carName;
}
//Cyclic Constructor
public Car(int carID, string carName, string carType,string carModel):this(carID,carName)
{
m_CarType = carType;
m_Model = carModel;
}
//Cyclic Constructor
public Car(int carID, string carName, string carType, string carModel,string color)
: this(carID, carName,carType,carModel)
{
m_Color = color;
}
}
static void main()
{
Car objCarA=new Car();
Car objCarB=new Car(1,"matiz");
Car objCarC=new Car(1,"matiz","SmallCar","2000");
Car objCarD=new Car(1,"matiz","SmallCar","2000","Dark Green");
}
Validation to Check for Comma separated EmailIDs
Regular Exp Description:
List of Email ids separated with [,] Email ID may contain character set as [._-']
Regular Expression
^((\w+([-_.']\w+)*@\w+([-_.']\w+)*\.\w+([-_.']\w+)*)*([,])*)*$
Regular expression Rules:
Finite automata rule Values should proceed with email Ids with Comma Separated. No comma will precede the email IDs.
Matches:
abc.xyz@anonymous.com
abc.xyz@anonymous.com,abc-xyz@anonymous.com,abc_xyz@anonymous.com
abc.xyz@anonymous.com,com,D'Souza@anonymous.com
Non-Matches:
abc.xyz
,abc.xyz@anonymous.com
abc.xyz@anonymous.com,
abc
Javascript
function CheckForCommaSeperatedEmailIDs( fieldValue )
{
var regex = /^((\w+([-_.']\w+)*@\w+([-_.]\w+)*\.\w+([-_.]\w+)*)*([,])*)*$/;
if( !fieldValue.match( regex ) )
{
alert('The Email IDs Invalid');
return false;
}
return true;
}
Validation to check UserID with Period/Dot seperated
Regular Expression Rules:
Finite automata rule, Values should precede with characters of set [A-Za-z] and followed with period(.) and character set [A-Za-z]Regular Expression:
^[a-zA-Z]+(\.[a-zA-Z]+)+$Matches
1) Ratan.Tata
2) Anil.Dhiru.Ambhani
Non-Matches
Ratan.
1) .Mukesh.
2) Amir.khan.
Regular Expression Logic in Javasctipt
| |||||||||||||||||
| Real Time Use Of Static Constructor if you look at above class it is an Utility class and it is consume by Business entity class instance say object Date that has minute component in it. If we have 10 screens that requires minutes to be displayed in dropdownlist in such cases rather then calling 10 calls to database or constructing this collection we prefer calling one instance at the very load of the application which in turns consume by all the pages and across all the users. In the process we have one instance available for all users and across pages. If one see in normal constructor ,one can notice it is invoked after instance is created whereas static constructor is invoked always first and when it is referenced. use System.collection.generics; public class Utility { public static IDictionary static Utility() { m_Minute=new IDictionary m_Minute.Add(1,"00"); m_Minute.Add(2,"15"); m_Minute.Add(3,"30"); m_Minute.Add(3,"45"); } public static IDictionary { return m_Minute; } }
Description :Below javascript code function returns false for entered special character and true for non special character.
Problem Statement:We have scenario where we have data stored in arraylist collection and want to pass this as data as input to Webservice method in string array format.
Namespace: System.collectionsSolution:
|
Sunday, March 10, 2013
Your Last chance Microsoft Virtual Academy
Join microsoft virtual academy for free . It has lot of online training courses which will help you develop your technical skills ,at the same time help you prepare one.
Benefits:
So hurry up!, You never know this may turns into paid one. Grab the opportunity and be one to rip benefit out of it. Share with this follow folks and friends . Help everyone.
Register now or never...
Benefits:
- Indirect trainings to appear for microsoft certifications.
- You develop your skill. Prepare strong foundation and clear your concepts and fundamentals.
- You get to know latest technology trends trainings in Vmware, Hyper v, Virtualization, Html5, Windows 8, Html ,mvc , mobile technology and many more. IOS,Android, Windows ..etc..
- You accumulate points to redeem for books, certifications or any valuable vouchers.
- You know where you stand.
- You get authentic transcripts of your courses.
So hurry up!, You never know this may turns into paid one. Grab the opportunity and be one to rip benefit out of it. Share with this follow folks and friends . Help everyone.
Register now or never...
https://www.microsoftvirtualacademy.com/GetStarted.aspx
Subscribe to:
Comments
(
Atom
)